Describe at Least Two Common Email Security Breaches
This is a very common cause of workplace injury encompassing everything from slipping on a wet. Weve all heard about them and we all have our fears.
What Is Email Security Best Practices For 2022 Upguard
Stats show that 4 in 5 breaches classified as a hack in 2012 were in-part caused by weak or lost stolen passwords.

. 2014 was a rough year for enterprise data security if the high profile breaches of Sony JPMorgan and Home Depot told us anything. Tripping slipping and falling. Compromised credentials describe a case where user credentials such as usernames and passwords.
8 common cyber attack vectors and how to avoid it 1. Control Access to Command Prompt. Weak and Stolen Credentials aka.
The username and password continue to be the most common type of access credential. In recent years ransomware has become a prevalent attack method. There are various state laws that require companies to notify people who could be affected by security breaches.
Prevent Windows from Storing LAN Manager Hash. Disallow Removable Media Drives DVDs CDs and Floppy Drives. This sort of security breach could compromise the data and harm people.
With this in mind I thought it might be a good idea to outline a few of the most common types of security breaches and some strategies for dealing with them. The leading cause of workplace injury in Australia. At about 24 percent of web attack attempts this was the second most common attack technique we witnessed.
To help your organization run smoothly. Adding security aspects after the enterprise architecture or system is designed and implemented will make the security solution complex. Here is the list of top 10 Group Policy Settings.
A security breach occurs when an intruder employee or outsider gets past an organizations security measures and policies to access the data. Important Group Policy Settings to Prevent Breaches. The 500000-record breach at Airway Oxygen Inc and the 697800-record breach at Commonwealth Health Corporation.
265 million discharged veterans records including name SSN date of birth stolen from the home of an employee who improperly took the material home Ensure proper physical security of electronic and physical sensitive data wherever it lives. Moderating Access to Control Panel. Hacking attacks may well be the most common cause of a data breach but it is often a weak or lost password that is the vulnerability that is being exploited by the opportunist hacker.
Here are the most common security threats examples. A security breach could be anything ranging from unauthorized access data leakage to misuse of the network resources. Data breaches are the most common but not all security incidents concern data theft.
In 2017 the worst year for healthcare security incidents in terms of the number of breaches reported there were 3286498 healthcare records exposed or stolen. A separate role for information security officer must be created to take charge of cyber security of the organization. It includes repetitive strain injuries and injuries incurred from lifting heavy objects.
The most common network security threats. The Security Breach That Started It All. There were two breaches involving more than half a million records.
Veterans Administration VA incident. Disable Forced System Restarts. For everyday Internet users computer viruses are one of the.
Examples of common workplace injury causes. Ive listed out 10 simple yet powerful steps you can take which will help in preventing disruptive cyber intrusions across your network. It was especially rough for ATT who suffered not one but two separate malicious insider attacks resulting in the exposure of customers social security numbers drivers license numbers and birth dates as.
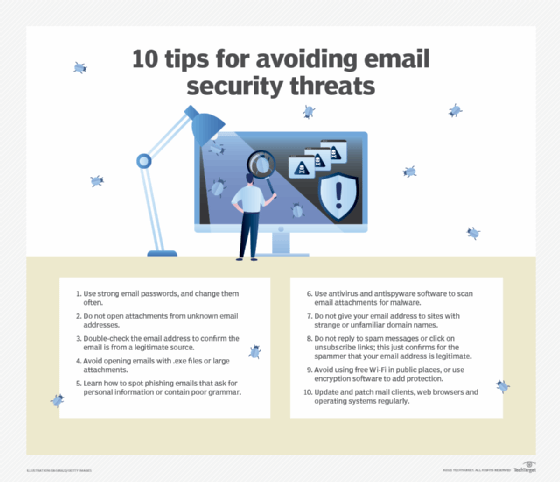
Strong password policy Brute force attacks are a popular form of cyber attack. The most common form of SQLi occurs when an attacker enters malicious SQL code into a field on a web page and the server-side code submits it to the database without properly sanitizing it first.

Email Security Email Security Cyber Security Awareness Cyber Security Technology
What Is Email Security Definition From Searchsecurity Com

What Is Email Security Definition Benefits Examples Best Practices Toolbox It Security

10 Best Practices For Email Security In 2021 Titanfile

4 Email Security Best Practices To Protect Your Organization In 2021 Easydmarc

Email Virus Complete Guide To Email Viruses Best Practices

Top 5 Threats To Email Security On Large Enterprises
![]()
10 Email Security Risks And How To Tackle Them 2022 Ees Corporation

What Is Email Security Definition Benefits Examples Best Practices Toolbox It Security
Different Types Of Email Security Solutions Can Help Prevent Phishing Attempts By Cybercriminals Duocircle
10 Email Security Risks And How To Tackle Them 2022 Ees Corporation
6 Types Of Email Threats And How To Mitigate Them Penta Security Systems Inc
Your Guide To Email Security And Risks The European Business Review
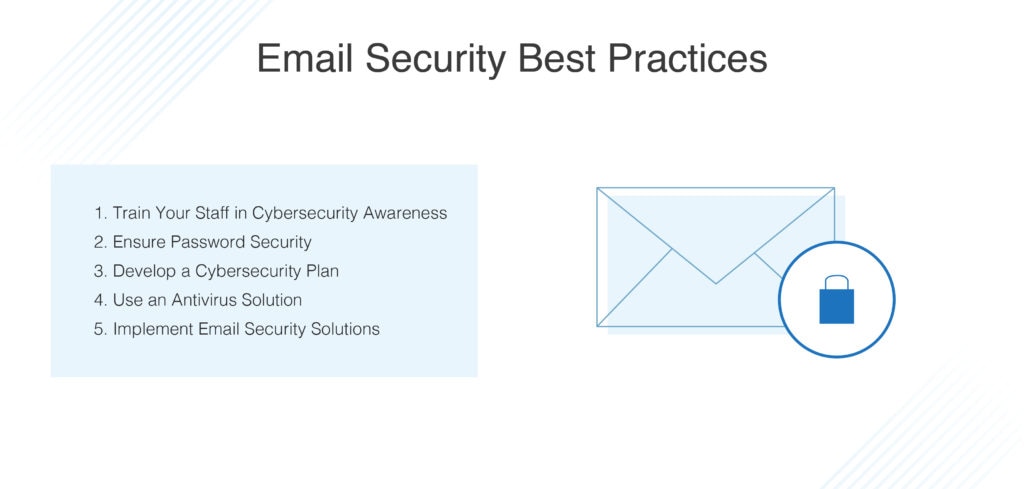
5 Email Security Best Practices For Businesses For 2022 Dnsstuff

What Is Email Security Definition Benefits Examples Best Practices Toolbox It Security

What Is Email Security Definition Benefits Examples Best Practices Toolbox It Security

How To Send Encrypted Email Hp Tech Takes

Top 5 Threats To Email Security On Large Enterprises
Your Guide To Email Security And Risks The European Business Review
Comments
Post a Comment